Multiple layers of access control and isolation defenses at every level of our platform, to protect your workloads from malicious activity.

Every virtual machine is fully isolated from all other VMs on the hostnode to prevent interference.
An agent runs onboard on every physical server to monitor and report any logins, suspicious activity, and resource hogging.
We revoke SSH access from our hosts to prevent them from looking at customer
Our IAM system allows you to manage who from your organization can access what and when, through our dashboard and API.
Background-checked employees
We vet all our team members during the hiring process, and we only provide hostnode access to those who need it.
3D Secure
We attempt 3D Secure authentication on every transaction to guarantee the cardholder is the one making the purchase.
KYC
We conduct KYC checks for those paying via other means, such as cryptocurrency. We carefully screen hosts to ensure trustworthiness and high uptime.
TLS Dashboard and API Encryption
We adhere by best security practices for encryption and authentication to prevent man-in-the-middle attacks and eavesdropping.



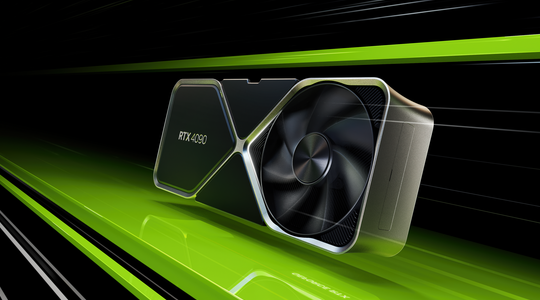
TensorDock aggregates GPUs from Tier 3/4 data centers with
certifications ranging from SOC 2, PCI DSS, ISO 27001, and HIPAA.
We hold our partners to 100% power and network SLAs to ensure
that your workloads are always available.
Access data centers with best-in-class security practices: reinforced walls, 24/7 surveillance,
biometric access control, and more.
Look for the "Data Center" badge on the deploy page.

We can tailor solutions to specific compliance
standards on a per-customer basis.
The industry's most cost-effective GPU cloud